introduction: this article is aimed at developers and systematically introduces the key points of deploying cloud servers in malaysia and how to interface with cloud service apis. the content focuses on network, instance configuration, certification, security and debugging, aiming to help engineering teams go online and operate in an efficient and localized manner.
why choose malaysia cloud server
deploying cloud servers in malaysia can help reduce cross-border delays, meet local compliance and data residency requirements, and make it easier to optimize network paths for southeast asian users. developers should evaluate target user distribution, legal requirements, and available areas to decide whether to launch in this area.
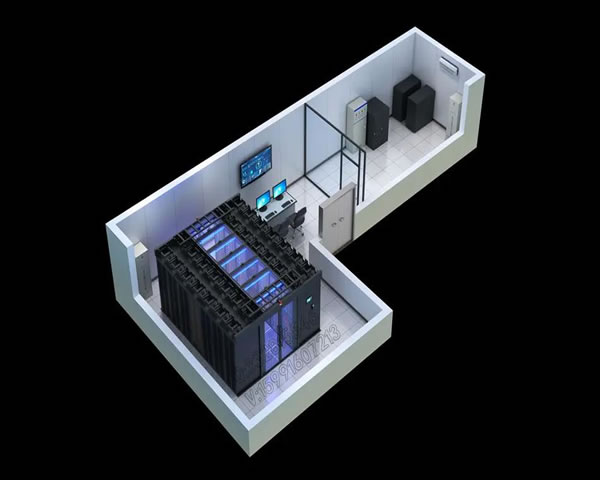
basic environment and network considerations
network planning must include public network bandwidth, private network architecture (vpc) and subnet division, routing and nat configuration. also consider cross-region dedicated lines or cdn access to improve access performance, and set up appropriate security groups and acls to control inbound and outbound traffic.
key points for instance configuration and region selection
when selecting an instance type, pay attention to the balance of cpu, memory, disk io and network performance, and adopt an elastic scaling strategy according to the load. the selection of regions and availability zones should take into account high-availability design to avoid single points of failure and ensure that backup and disaster recovery strategies cover the target area.
storage, backup and security group policies
the storage solution needs to distinguish between block storage and object storage, properly design hot and cold data strategies, and perform snapshots or backups regularly. in terms of security, role-based access control, the principle of least privilege, and intrusion detection and log auditing mechanisms should be enabled to meet compliance requirements.
how to interface with the api: overall steps
interfacing with cloud service apis usually includes registering an account, creating api credentials, reading interface documents, testing calls, and integrating the api into the ci/cd process. developers should first complete end-to-end call verification in the test environment before enabling monitoring and alarming in the production environment.
identity authentication and key management
common methods for api authentication include key-based signatures, oauth, or temporary credentials. keys should be stored using a secure key management service and rotated regularly, while using a least privilege policy between services to reduce the risk of credential compromise.
common api call examples and debugging suggestions
common calls include instance creation, image management, network configuration and monitoring data pulling. when debugging, it is recommended to turn on detailed logs, use simulated request tools and retry strategies, and add interface contract testing to ci to prevent version compatibility issues.
network optimization and delay monitoring practice
continuously monitor network latency and packet loss rates, and use probes and apm tools to locate performance bottlenecks. delays can be reduced through route optimization, enabling cdn, compressed transmission and connection reuse to ensure a stable user experience for malaysia and surrounding areas.
summary and suggestions
summary: to successfully deploy and interface with apis in malaysia, developers should invest in planning and automation in constituencies, networking, security, certification and testing. it is recommended to fully verify in the sandbox environment first, then gradually go online and introduce monitoring and disaster recovery mechanisms to ensure stable operation.

- Latest articles
- Security And Backup Solutions For Enterprise-level Websites Using The Us Cn2 Site Group
- A Comprehensive Explanation Of The Relationship Between How Much A Cambodian Cloud Server Costs And Its Performance Indicators
- Analysis Of The Difference In Latency And Packet Loss Rate Between Singapore Dedicated Vps And Ordinary Vps
- How To Use Vietnamese Native Ip Servers To Build Stable Corporate Email And Application Services
- Comprehensive Comparative Analysis Of Stability And Cost-effectiveness Between Cambodia Cn2 And Other International Dedicated Lines
- Detailed Description Of Malaysia Vps Cn2 Gia Multi-node Backup And Security Protection Strategy
- Compare The Cost Performance Of Servers Rented In Japan In Different Computer Rooms.
- Hong Kong Alibaba Cloud Server Bandwidth Monitoring Methods And Key Points For Setting Alarm Thresholds
- Practical Tips For Cost-saving When Cross-border E-commerce Deploys Cera Us High-defense Servers
- Steps, Risk Management And Optimization Strategies For Enterprises To Migrate To German Server Hosting
- Popular tags
-
Discuss The Best Purchasing Channels For Malaysian Cloud Servers
This article discusses the best purchasing channels for cloud servers in Malaysia, analyzes the characteristics and advantages of different service providers, and helps users make informed choices. -
Performance And Security Evaluation Of Malaysian Cloud Servers
This article evaluates the performance and security of Malaysian cloud servers to help enterprises and individuals choose the right server. -
Detailed Explanation Of Malaysia’s Vps Security Assessment And Compliance Requirements
provides a detailed explanation of malaysia's vps security assessment and compliance requirements, covering legal compliance, technical controls, identity and access management, log auditing, vulnerability management, supplier due diligence and disaster recovery strategies, to help enterprises achieve safe and compliant vps deployment in the malaysian environment.